
Relocating IT systems within a financial organization requires a level of discipline that goes far beyond a typical office transition. Every system has sensitive data about transactions, client records, compliance reports, and how the business runs. Even a little break in handling can create problems that need a lot of time and work to fix.
A well-planned IT relocation helps companies keep control of their systems and keep important data safe. It helps teams progress through each stage clearly, knowing that security, compliance, and operational continuity are all still in sync.
This blog explores how financial organizations can approach IT relocation with a strong focus on financial data protection, stable network infrastructure, and reliable project management practices that support long-term success.

Why Financial Data Protection Matters During IT Relocation
Financial information is what builds trust between a company and its customers. It helps with everything from day-to-day transactions to long-term reporting and compliance duties. When IT relocation occurs, this data leaves its customary safe place for a short time, which makes it more vulnerable.
If you don't plan ahead, the standard safety measures can be thrown off when systems are unplugged, moved, and then restored. This means that financial data protection is the most important thing to do during the whole process.
Organizations that invest time in protecting their data during IT relocation often experience smoother transitions and fewer complications. They maintain confidence across internal teams and external stakeholders, while also reducing the likelihood of compliance issues.
“Financial data protection also helps make sure that rules are followed. In Canada, businesses are obligated to treat personal and financial information in the same way, even if systems are running or being changed. Because of this assumption, it's important to treat IT relocation as a regulated and well-documented operation.”
Key Risks to Financial Data During IT Relocation
Organizations can better prepare for and avoid frequent problems that come up during IT relocation by knowing what risks might happen. Each step has its own problems, especially in places where systems are linked together.
Data Loss During System Disconnection
It's always possible that some data won't be captured correctly when systems are shut down. If backups aren't comprehensive or dependencies are missed, records or data may be lost or corrupted.
Transaction logs, databases, and reporting tools are just a few of the many types of data that financial systems use. If these layers aren't managed carefully, it might be hard and take a long time to go back to normal. This is why financial data protection must begin before any system is disconnected.
Unauthorized Access in Transit
Transporting physical hardware introduces a different type of risk. Devices that contain sensitive information may be exposed if access is not tightly controlled.
During IT relocation, hardware may pass through several stages before reaching its destination. Without clear oversight, there is a chance that unauthorized individuals could interact with these systems. Maintaining strict control during this phase is essential for financial data protection.
Network Infrastructure Gaps
When systems are disconnected and reinstalled, there may be temporary gaps in the network infrastructure. If security settings aren't restored correctly, these gaps can make things less safe.
Even a short time without protection might make systems more vulnerable to attackers. This is why careful planning and testing are required to maintain a secure network infrastructure throughout IT relocation.
Lack of Structured Project Management
Coordination between teams might become erratic without good project management. Things may take longer than planned, duties may overlap, and essential steps may be missed.
An organized way to handle project management makes everything clear and keeps the whole IT relocation on track. It keeps the focus on financial data protection and makes sure that each step is done in the right order.
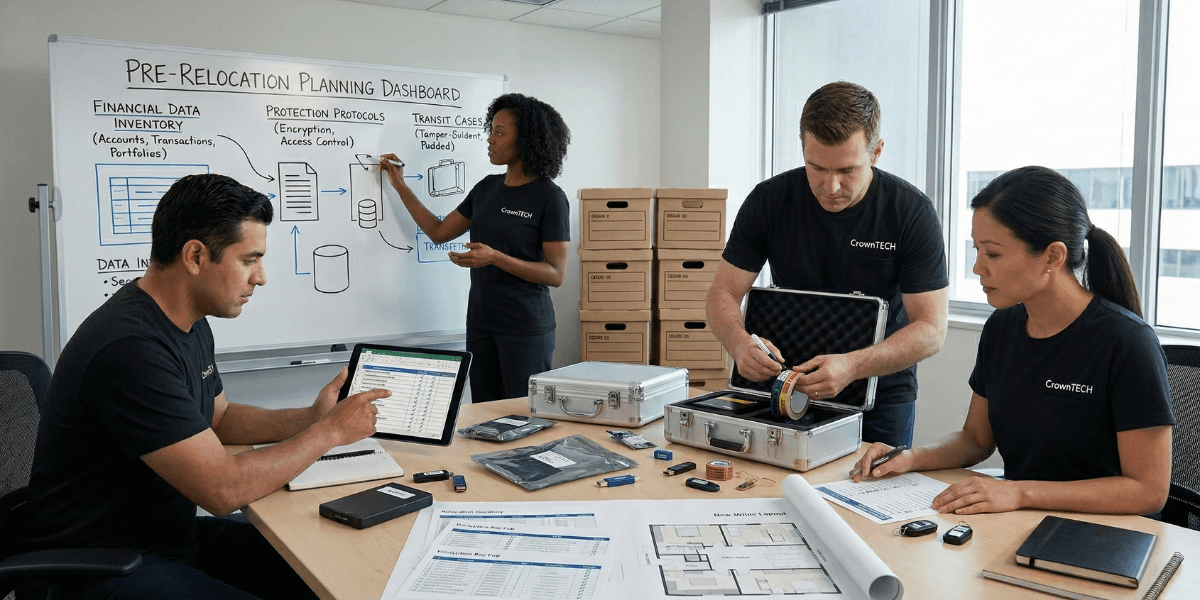
Pre-Relocation Planning for Financial Data Protection
Preparation plays a defining role in the success of IT relocation. A well-prepared organization can move through the process with confidence, while a lack of planning often leads to unnecessary complications.
Implement a Reliable Backup Strategy
Backups provide a safety net that protects against data loss. A structured approach helps maintain confidence that information can be recovered if issues arise.
- Maintain three separate copies of all critical data
- Store data across two different types of storage media
- Keep one copy in a secure off-site location
This approach creates redundancy and strengthens financial data protection across the entire IT relocation process.
Conduct a Full Data Audit
A full data audit helps businesses find out where important information is kept and how it is used. Financial data is generally spread out among several platforms, such as servers, the cloud, and backup storage.
By mapping out all of their data sources, teams can see clearly what requires to be kept safe. This helps financial data protection better and ensures that resources are used wisely during IT relocation.
Define Access Controls Early
Controlling who can access systems is a critical part of preparation. Before IT relocation begins, access should be limited to essential personnel.
Clear access policies reduce the likelihood of unauthorized interactions with sensitive data. They also help maintain accountability, which supports financial data protection and compliance requirements.
Securing Data During IT Relocation
Once systems are prepared, attention shifts to maintaining control throughout the relocation process. Each step must be handled with consistency to protect both data and infrastructure.
Use End-to-End Encryption
Encryption acts as a protective layer that keeps data secure even if systems are accessed without authorization. During IT relocation, encryption should be applied to all sensitive data.
This approach strengthens financial data protection by ensuring that information remains unreadable to unauthorized users. It also provides an additional safeguard during transportation and system transitions.
Maintain a Strict Chain of Custody
Tracking every asset is essential when handling financial systems. Each device should be documented at the time of disconnection and again upon arrival at the destination.
This process creates a clear record of who handled each piece of equipment and when. It supports accountability and provides valuable documentation for compliance reviews.
Working with experienced providers like CrownTECH® helps maintain consistency in chain-of-custody practices.
Secure Transportation of Hardware
Physical handling plays a major role in financial data protection. Servers, storage devices, and other components must be transported with care.
Proper handling reduces the risk of damage or loss while maintaining control over sensitive systems. It also supports the integrity of the IT relocation process.
Protect Remote Access During Transition
During IT relocation, employees may need to access systems remotely. This introduces additional considerations for financial data protection.
- Use secure VPN connections for all remote access
- Enable multi-factor authentication for user accounts
- Limit system access to essential personnel only
These actions help keep things safe even while teams are operating outside of the main office.
Compliance and Regulatory Considerations in Canada
There are rules that financial organizations have to follow that affect how they manage data. To stay in compliance, IT relocation must meet certain standards.
Understanding PIPEDA Requirements
PIPEDA outlines how personal information should be handled across Canada. During IT relocation, organizations must continue to protect data with the same level of care as during normal operations.
This includes controlling access, maintaining documentation, and protecting data throughout transportation and reinstallation.
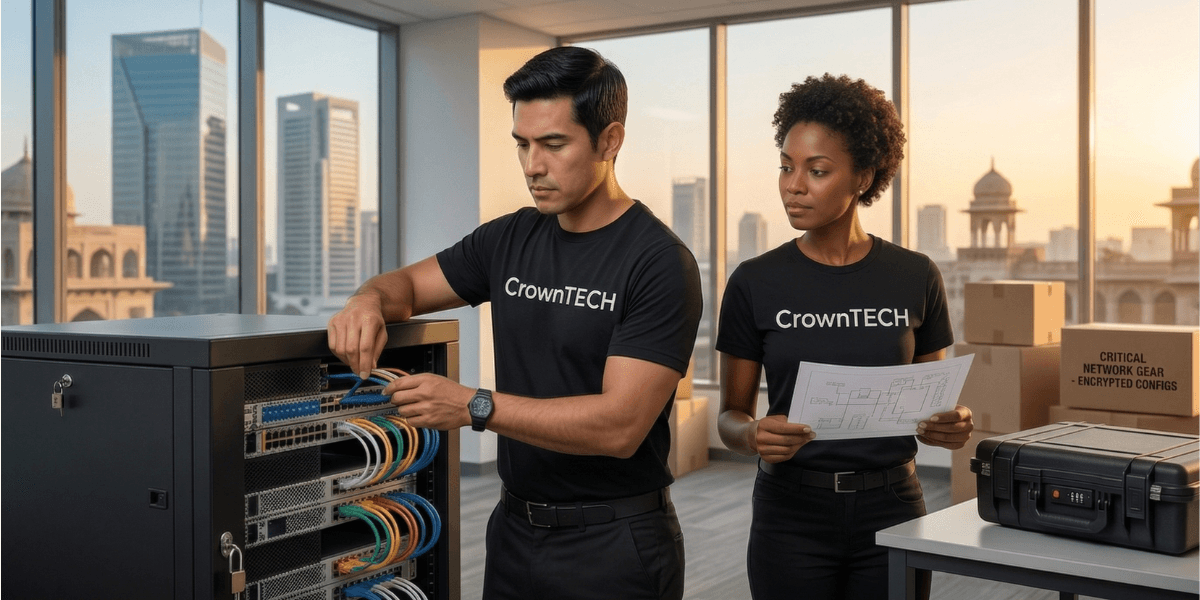
Role of Network Infrastructure in Secure IT Relocation
The backbone of IT systems is the network infrastructure. It is very important to keep both performance and security during IT relocation.
Testing Before Full Operation
Testing provides confirmation that systems are functioning correctly and securely.
- Verify connectivity across all systems
- Check data integrity within applications
- Review security configurations and controls
This step helps confirm that IT relocation has been completed successfully and that systems are ready for full operation.
Pre-Relocation Network Preparation
The environment must be carefully prepared before systems can be put in at the new location. This means looking at things like how well things link, how they are laid out, and how much power they need.
A well-planned network infrastructure helps the IT relocation process go more smoothly and cuts down on delays. It also helps keep things stable after the systems are back up and running.
Secure Configuration During Setup
When systems are reconnected, configurations must meet tight security rules. You should set up firewalls, access controls, and endpoint protection correctly.
A secure network infrastructure protects financial data by making systems less vulnerable and keeping them working properly.
Importance of Project Management in IT Relocation
Project management gives you the framework you need to plan and carry out a complicated IT relocation. It keeps teams on the same page and lowers the chance of making mistakes.
Coordinating Teams and Responsibilities
IT relocation involves many teams, such as IT workers, compliance teams, and outside vendors. Consistent communication is easier when it is clear.
Project management makes sure that everyone knows what their responsibilities are and that tasks are done in the right order.
Managing Risk Throughout the Process
Teams can deal with dangers before they become big problems if they find them early. This helps preserve financial data and cuts down on interruptions.
A structured approach helps maintain control and keeps the IT relocation process predictable.
Maintaining Detailed Documentation
Documentation makes it possible to see every step of the IT relocation procedure. It helps firms assess their procedures and meet regulatory standards.
Accurate records also contribute to improved planning for future relocations.
How CrownTECH® Supports Secure IT Relocation
Because their systems are so complicated and they have to follow so many rules, financial firms need a high level of accuracy. An organized and disciplined strategy helps you stay in charge and keep sensitive information safe.
CrownTECH® brings extensive experience in handling IT relocation for financial environments. Their approach focuses on consistency, accountability, and strong financial data protection across every stage.

Compliance-Driven Planning and Scoping
Before IT relocation, you need to have a clear picture of the company's systems, dependencies, and rules. This means making sure that processes are in line with rules like PIPEDA and PCI-DSS.
With this level of planning, teams can go forward with confidence while keeping their financial data protection.
Detailed Documentation of Systems and Infrastructure
Before moving, each system is meticulously recorded. This covers settings, dependencies, and needs for the system to work.
This precise method helps set up the system correctly at the new location and lowers the chance of mistakes during the IT relocation.
Secure Chain of Custody for All Data Assets
All data-bearing assets are tracked throughout the process. Each transfer is recorded, creating a clear chain of custody.
This provides accountability and supports financial data protection in regulated environments.
Controlled Handling of Network Infrastructure
During an IT relocation, the network infrastructure is handled with care. To keep the system's integrity and performance, each part is carefully monitored.
This approach supports stable operations and reduces the risk of configuration issues.
Structured Project Management Throughout the Process
A structured project management approach keeps the process organized and aligned. Timelines, responsibilities, and risks are continuously monitored.
This level of coordination supports financial data protection and ensures consistent execution.
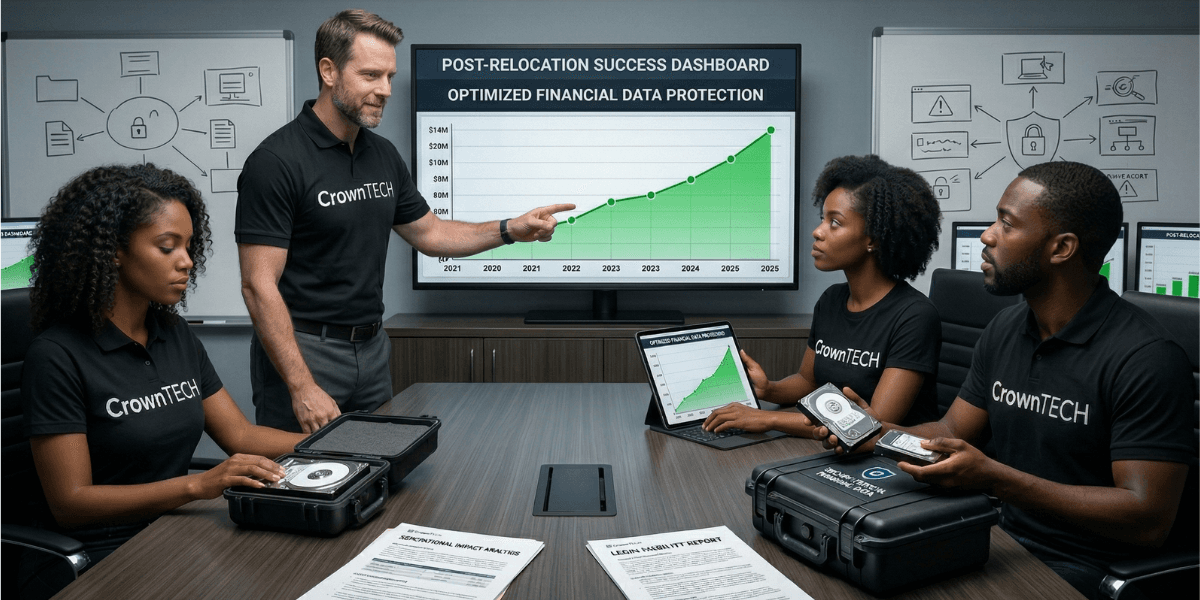
Post-Relocation Validation and System Verification
After systems are reinstalled, they are put through a lot of tests. This includes checking the performance of the network infrastructure, access controls, and data integrity.
This last stage makes sure that the IT relocation went well and that the systems are ready to be used.
Conclusion
A successful IT relocation depends on careful preparation, disciplined execution, and a strong focus on financial data protection. Each phase contributes to maintaining stability, protecting sensitive information, and supporting compliance requirements.
With a clear strategy, reliable network infrastructure, and structured project management, organizations can approach IT relocation with confidence and control.
If your organization is planning an upcoming IT relocation, connect with CrownTECH® to build a secure and well-structured approach tailored to your environment.