Relocating IT systems in a healthcare environment carries a unique level of responsibility. Every server, workstation, and network component supports patient care in some way, and each one may store or process sensitive information. When systems relocate, the risks shift as well. A poorly managed transition can interrupt clinical workflows or expose confidential data.
This is where a planned approach to IT relocation becomes very important. Healthcare organizations require a clear plan that keeps systems safe, helps workers, and keeps things running smoothly. Every step, from preparation to final approval, helps keep trust and stability. In this blog, we’ll explore practical strategies that help healthcare teams relocate IT environments while maintaining strong healthcare data protection and consistent performance.
Understanding the Risks in Healthcare IT Relocation
Healthcare environments rely heavily on technology. Systems manage patient records, diagnostics, communication, and treatment coordination. When considering an IT relocation for healthcare, the risks go beyond only technical problems and can have a direct impact on patient outcomes.
Patient-Centred Impact
Healthcare systems operate in real time. Doctors, nurses, and administrative teams depend on immediate access to accurate information. If systems are down for even a short time during a relocation, workflows can slow down and important decisions may be put off. That's why every relocation needs to fit in with clinical timelines and priorities.
Data Sensitivity and Responsibility
Patient data carries a high level of sensitivity. Maintaining data privacy in healthcare is a continuous responsibility that does not pause during relocation. To keep anyone from getting into devices without permission, they must be treated carefully, whether they are still in use or not.
Operational Complexity
Healthcare facilities often have interconnected systems. Servers, applications, and network infrastructure must function together seamlessly. Any disruption in one area can affect multiple departments, which increases the importance of careful coordination and strong project management.
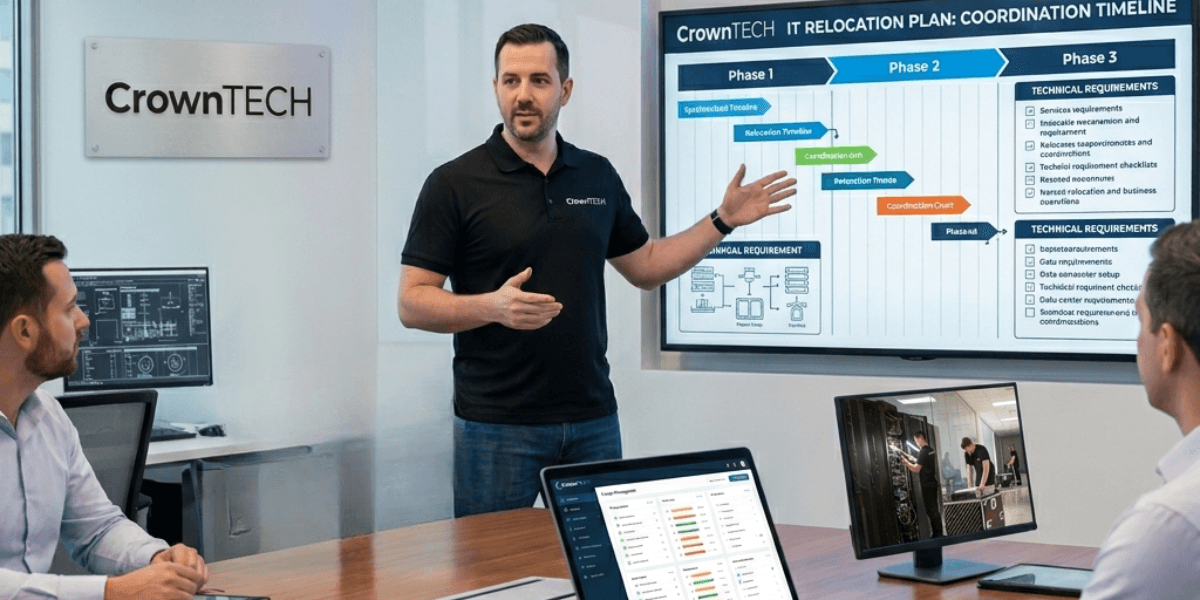
Laying the Groundwork with Strategic Planning
A successful relocation begins with a solid plan. Teams need to know their surroundings, spot threats, and set clear priorities before they may disconnect any equipment. This step sets the mood for the whole process of IT relocation.
Comprehensive Risk Assessment
A detailed assessment helps uncover potential vulnerabilities and prepares teams for challenges ahead. This means looking at the physical, technical, and administrative parts of the environment.
- Identify systems that store or process sensitive data
- Evaluate existing security controls and access permissions
- Review dependencies across applications and network infrastructure
- Analyze risks related to transportation and handling
This level of planning helps stronger healthcare data protection throughout the relocation.
System Prioritization
Not every system requires the same level of urgency. During IT relocation for healthcare, prioritizing systems helps maintain continuity and reduces disruption.
First, you should fix critical systems including electronic health records, patient monitoring tools, and prescription systems. Next come secondary systems like imaging platforms and tools for communicating within the company. After basic services are solid, you can work on administrative systems.
Timeline and Coordination
Creating a realistic timeline allows teams to coordinate tasks effectively. Strong project management helps align schedules, assign responsibilities, and track progress. This makes things less confusing and maintains the relocation process orderly from beginning to end.
Protecting Data Before the Relocation Begins
Before equipment leaves its original location, data protection measures must already be in place. Preparing systems in advance helps reduce risks and creates a safer environment for transition.
Access Control Measures
Controlling who can access systems during relocation is critical. Only authorized personnel should handle equipment or interact with data. Clear access policies help maintain data privacy in healthcare and prevent accidental or intentional misuse.
Encryption and Data Security
Encryption is still one of the best ways to keep private information safe. All data should be encrypted when it is stored and when it is sent. This add an extra layer of security that limits exposure even if someone gets to the actual device.
Healthcare organizations that prioritize encryption strengthen their approach to healthcare data protection and reduce the likelihood of breaches.
Data Cleanup and Reduction
Less data makes relocating easier and less risky. You should delete or securely archive files that are no longer needed, applications that are no longer used, and data that is no longer needed. This approach limits the amount of sensitive information being relocated.
A cleaner system environment also improves efficiency during IT relocation and supports faster system validation after installation.
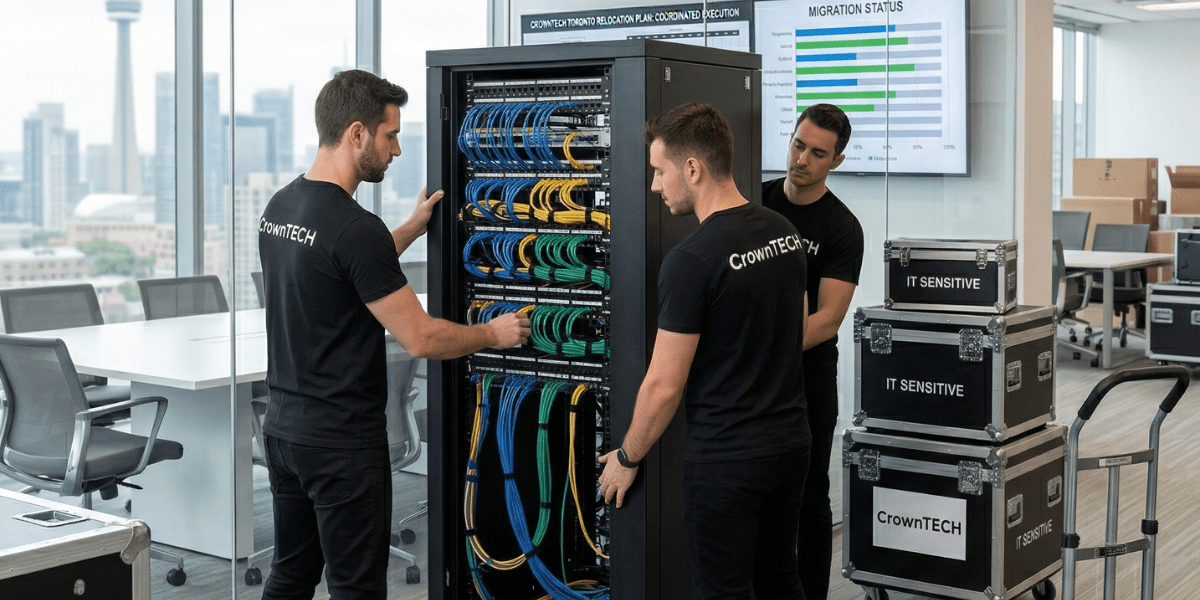
Maintaining a Secure Chain of Custody
Once systems are prepared, tracking them throughout the relocation becomes a top priority. A well-documented chain of custody provides visibility and accountability at every stage of the relocation.
Controlled Handling Procedures
Only trained and authorized people should be able to use the equipment. Giving specific people responsibility makes things less confusing and makes them more accountable.
- Each device is logged before removal
- Assigned personnel manage handling and transport
- Arrival and installation are verified and recorded
This structured approach supports consistent healthcare data protection.
Detailed Documentation
Every step of the process should be recorded. This includes disconnection, transport, and reinstallation. Accurate records help organizations track assets and demonstrate compliance with security standards.
Documentation also supports effective project management, allowing teams to monitor progress and address issues quickly.
Secure Transportation
Transportation plays a critical role in maintaining system integrity. Vehicles used for IT relocation for healthcare should be monitored and equipped with security features. GPS tracking, restricted access, and careful handling practices help reduce risks during transit.
Strengthening Physical and Environmental Security
Relocation can affect both your equipment and your data in physical ways. To keep a system reliable, it's important to protect hardware against environmental dangers.
Equipment Protection
Servers and networking devices require stable conditions. Proper packaging, shock absorption, and temperature control help prevent damage. Protecting physical assets also protects the network infrastructure that supports healthcare operations.
Monitoring and Visibility
Tracking systems during transportation give you real-time information about the location and condition. Monitoring tools help teams deal with problems that come up fast. This level of visibility supports a smoother IT relocation process.
Controlled Access During Transit
Limiting access to equipment reduces the chance of unauthorized interaction. Only designated personnel should have access to systems during transportation. This helps maintain strong data privacy in healthcare throughout the journey.
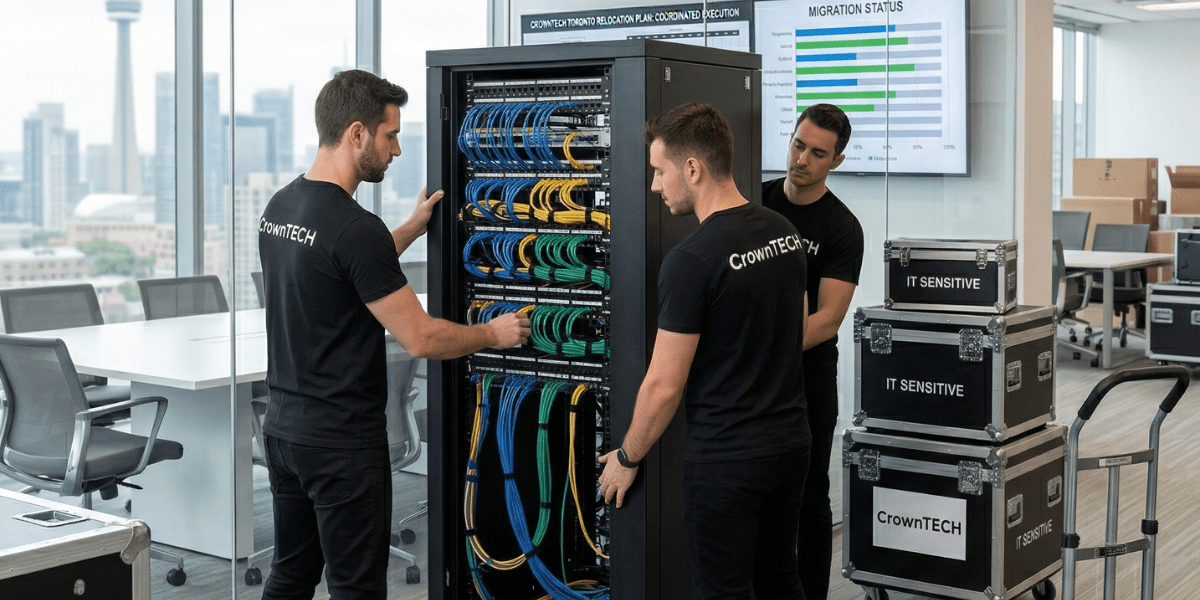
Reinstallation and Post-Move Validation
Once systems get to their destination, they need to be carefully reinstalled and tested. At this point, you can be sure that everything is working properly and that no data has been lost.
Final Audit and Reporting
A post-move audit confirms that all systems are accounted for and operating as expected.
- Verify inventory against initial records
- Review chain-of-custody documentation
- Identify and resolve any discrepancies
- Document final system status
Strong project management helps keep this phase organized and thorough.
System Testing and Verification
Each system should be tested before it becomes operational. This includes checking data integrity, verifying application performance, and confirming connectivity. These steps reinforce healthcare data protection and help detect issues early.
Rebuilding Network Infrastructure
When you change the network infrastructure, you need to pay attention to the little things. Before users can get back in, the systems must be correctly connected, divided up, and secured. A robust network environment helps workflows run smoothly and communication stay reliable.
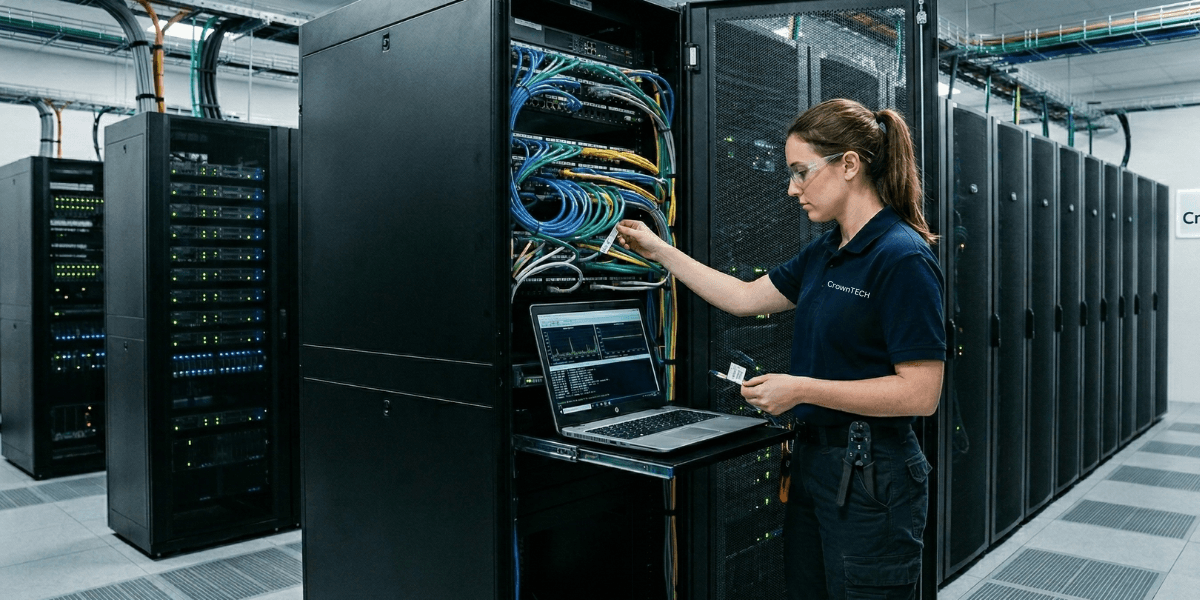
The Value of Experienced IT Relocation Providers
Healthcare IT relocation requires specialized expertise. Working with experienced providers can simplify the process and reduce risks significantly.
Organizations like CrownTECH® bring structured methodologies and deep industry knowledge to each project. Their approach to IT relocation for healthcare focuses on maintaining operational continuity while protecting sensitive data.
Experienced teams understand how to coordinate complex environments, manage timelines, and maintain compliance standards. Their involvement helps healthcare organizations complete relocations with confidence and clarity.
Preparing for Evolving Compliance Standards
Healthcare regulations continue to evolve, and organizations must adapt their practices to stay aligned with new expectations. Preparing for future changes helps maintain strong data privacy in healthcare.
Strengthening Internal Processes
Organizations keep ready by regularly updating their internal policies. Better outcomes during IT relocation come from better staff training, updated documentation, and stronger security practices.
Adopting Advanced Technologies
Modern tools can enhance relocation processes. Automated tracking systems, advanced encryption methods, and real-time monitoring solutions improve both efficiency and security.
Continuous Improvement
Learning from each relocation project helps refine future strategies. Reviewing performance, identifying areas for improvement, and updating processes support long-term success.
Common Challenges and How to Overcome Them
Even with careful planning, challenges can arise during relocation. Understanding these challenges helps teams prepare effectively.
Managing Downtime
Downtime can affect patient care and operational efficiency. Careful scheduling and strong project management help reduce disruptions and maintain continuity.
Protecting Sensitive Data
Maintaining healthcare data protection requires constant attention. Encryption, access control, and secure handling practices help reduce risks.
Coordinating Multiple Teams
Relocation often involves multiple departments and vendors. Clear communication and structured planning support smoother collaboration during IT relocation for healthcare.
Conclusion
Healthcare IT relocation requires careful planning, disciplined execution, and a strong focus on protecting sensitive information. Each step, from preparation to final validation, plays a role in maintaining system reliability and safeguarding patient data.
With the right strategy and experienced support from providers like CrownTECH®, organizations can relocate their IT environments with confidence while maintaining strong IT relocation standards and consistent performance.
If you are planning a healthcare IT relocation and want a structured, secure approach, contact us today to start building a relocation plan that supports your systems, your staff, and your patients.